Is this a genuine email or is it a fake designed to deceive recipients into giving up confidential information? Email is the source of more than 93% of all cybersecurity events, so having an understanding of how these phishing attacks work can prevent account takeover leading to identity theft, bank fraud, loss of intellectual property, and disruption of business operations.
Many of these examples below work by tricking the recipient into clicking a link or opening an attachment. Attackers want to steal your information, and dangerous attachments are a simple way to achieve that.
Other examples are more targeted - spear-phishing attacks that are designed to reach a specific user based on what the attacker learned about them. These attacks may use information about your employees or company to make their messages even more persuasive.
This article will examine some real-life examples of malicious emails quarantined by Guardian Digital EnGarde Cloud Email Security Solution and the signs that indicate these emails are fraudulent. We also offer tips for recognizing and defending against malicious emails that frequently lead to damaging attacks and breaches.
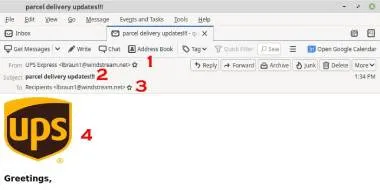
Parcel Delivery Updates!
This email starts with a message letting you know that your package is on its way, and provides info on how to find more delivery info by downloading an eVoucher attached to the email.
This is a phishing attempt we caught that tries to use our familiarity with common brands (1 & 4) to gain the trust of the recipient and lower our guard enough to click the file attached to the email. Once the recipient opens and clicks on the attachment, a javascript application runs on the victim's computer, building a backdoor to the cyber criminal’s network where they can take control of the computer to be used in other attacks.
How to tell this email is a fraud:
- From address does not contain an actual UPS domain
- Subject lacks capitals or proper punctuation
- Body contains very generic language, not specifically addressing any particular recipient
- Recipient address is just “Recipients” without being addressed to anyone specific
- Poor grammar, lack of capitalization in the subject and body
- UPS tracking emails contain tracking info in the body, not as an attachment
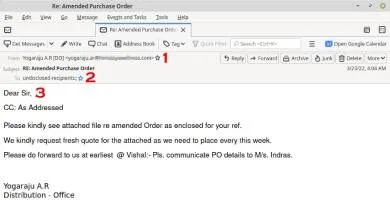
Amended Purchase Order
This email contains what appears to be an updated purchase order. If you were anticipating a purchase order, you may be more inclined to investigate further to see if this was it. You’ll notice it’s very nondescript, which may motivate the recipient to click the attachment to find out more.
This is the result of an account takeover attack. This email was sent from a legitimate account after the victim’s identity was stolen and the cyber criminal used their credentials to send emails to recipients that contain malicious attachments that execute spyware on the recipient’s computer.
How to tell this email is a fraud:
- Email sent from an unfamiliar contact
- Sent to unknown recipients
- Generic salutation
- Attachment contains an executable file within an archive
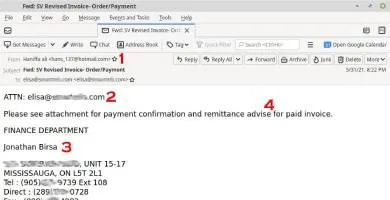
Revised Invoice Order/Payment
If your job regularly involves reviewing purchase orders or payment information, this email may appear to be just like every other. This email appears to have an invoice attached. The sender looks like a legitimate address from a legitimate business.
This is the "Proof Of Payment" phishing scam that’s designed to convince you to click the attachment and enter your login credentials in the resulting web page.
The attachment is opened in the victim’s browser, which then presents a login page which leads the user into believing a spreadsheet would appear upon a successful login.
Instead, your login credentials are sent to a compromised Wordpress site. Once the attacker has your login credentials, they will use them to attempt to login to your social media sites or business email accounts.
Opening attachments from unknown senders is never a good idea, but even legitimate senders can have their account compromised then send malicious attachments.
How to tell this email is a fraud:
- Email sent from an unknown “freemail” account, not a real business address
- No salutation - only a generic automated greeting with an email address
- Email is signed from a name different than the sender
- Body content contains common spelling errors
- Attachment contains a non-specific HTML file
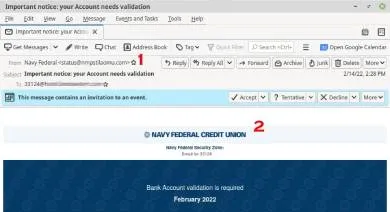
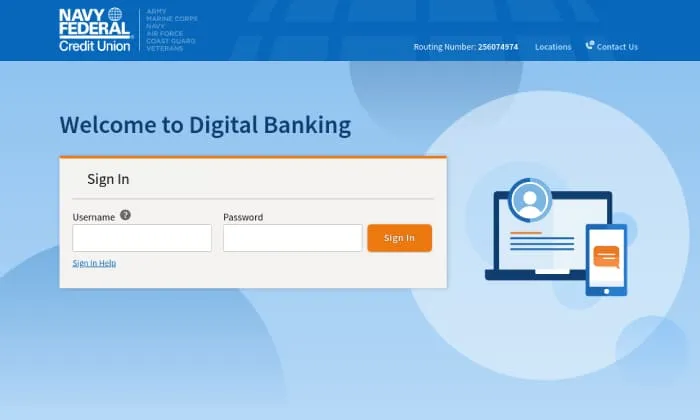
Verify Your Navy Federal Credit Union Credentials
You’ve received an email from your credit union, instructing you to verify your login credentials for fear of losing access to your account or concerned about the potential for fraudulent charges being posted to your account.
This email appears to have originated from the real Navy Federal Credit Union, complete with a near identical copy of a legitimate NFCU email containing a logo and other details indistinguishable from a real NFCU email. It uses a sense of urgency to implore the recipient to act quickly or severe consequences will result.
However, this spear-phishing email and the included attachments are designed to trick the recipient into providing their login details to the threat actor, who can then use your credentials to login to the real NFCU website on your behalf, siphoning your finances into their own bank account.
Clicking on the attachment leads the victim to an NFCU website login page that’s also indistinguishable from the login page actual NFCU clients use to login. It’s never a good idea to login to a website by clicking a link in an email. Enter the website directly into your browser’s location bar instead.
The login page is an exact mirror of the actual NFCU login page, except it’s been changed to send your credentials off to the bad actor once you click “Submit.” These fake login pages are many times prepackaged on the dark web for cyber thieves to purchase, then downloaded and modified to be used on a website they have compromised for this purpose.
How to tell this email is a fraud:
- Email appears to be from “Navy Federal,” but the email address is a random unknown domain. The email address in the “From” field of an email is very easily manipulated and can’t be trusted, but an especially strange one can be an indication of fraud.
- Email body makes outrageous claims about the member account being suspended or even deleted automatically. This email also lacks any specifics about the user, only their email address without a username or account info.
- Banks and Credit Unions do not send attachments that require the recipient to open to complete a form or execute a command
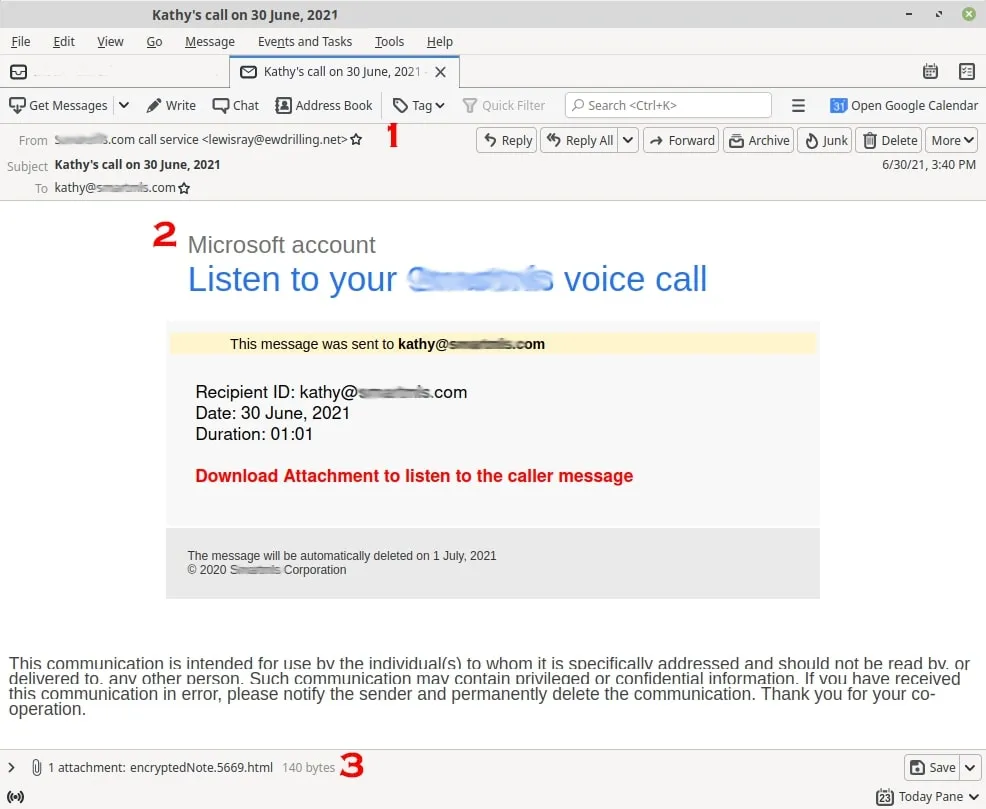
Listen to Your Voice Call
You’ve received an email that appears to contain an attachment with a recent voicemail included. Voicemail is a tool familiar to all of us, and most major service providers will allow you to receive your voicemail in an email. If you’re in a hurry, or expecting a voicemail, this may seem like a legitimate request. It also uses common brands, helping to boost the email’s legitimacy.
However, these emails are a convenient trojan horse for malicious attacks like this one and may not raise any alarm bells. This is a mass-scale operation that sends thousands of emails at a time, designed to catch someone at just the right time. This email is designed to promote a phishing website used to harvest account credentials from its victims. Once the victim enters their account credentials, the bad actor then uses these credentials on legitimate sites (social media, banking, corporate accounts, cloud services) in an effort to take over the victim’s identity, siphon money from their account, or use it to gain entry into an organization.
How to tell this email is a fraud:
- Generic From address contains unrecognizable sender with no relation to any voicemail service
- Email body contains no specific information about the recipient
- Opening unknown or dubious attachments included in emails should be avoided. Special attention should be given to any website resulting after opening the attachment to be sure it is legitimate and associated with the company providing the service.
Here are some ways to recognize malicious emails:
Cybercriminals are finding new and more sophisticated ways of exploiting a business’s vulnerabilities and breaking into their systems. Because of this, it is important to be be able to spot indicators that an email is fake, including:
- Check the sender's email address: If the sender's email is not an official address, it may be a phishing email. An official looking email address doesn’t necessarily mean that it’s official, but a random email address with no relation to the legitimate sender should be treated with caution. Hover or click the email address to try and expose more details about the sender.
- Look for spelling, punctuation, and grammar mistakes. Official emails should be free from common grammar mistakes. Pay particular attention to phrasing in the email, as many phishing scammers know English as a second language.
- Check links before clicking on them: Scammers will link to a phishing website with a domain that may look similar to the official domain, but one of the characters may be replaced with a similar character. Hover over any links to have them displayed in your email client before clicking to verify they are actually going to the genuine website.
- Think about what the email asks for: legitimate organizations will never request your Social Security number or other account details via email.
- Look at the greeting: If the email is legitimate, you will be greeted by your name and not by something generic like "Dear Member" or "Dear User."
- Take a close look at any images used: Scammers may spend some time on making the emails look right but may not have the graphic design skills to recreate the official images correctly. Some images may appear blurry, skewed, or just not right. Emails impersonating a brand may contain a brand image, but lack the full header or colors or style of the brand.
- Avoid clicking links in phishing emails. Clicking links makes you a higher target - it affirms with the attacker that the email reached an actual recipient. Clicking malicious links may also compromise your computer by launching an application or infecting it with malware, sometimes without you even knowing.
- Don’t be provoked by a sense of urgency. Take your time. Think before you act.
- Avoid opening attachments in emails. Desktop antivirus scanners may not be aware of the risks of opening a particular website from an attachment. Opening an attachment in a phishing email can spread malware, such as ransomware, to activate locking up your computer and encrypting documents to block access.
Avoid clicking links in emails that:
- Are not addressed to you specifically
- Are from businesses that you were not expecting to hear from
- Contain poor grammar and spelling
- Lack any personal details to identify you specifically as the recipient
- Include links to a random URL that is not associated with the company related to the email itself
What if I have fallen victim to one of these scams?
If you’ve clicked on a malicious link, provided your login details to what you now believe to be a rogue website, inadvertently installed and executed malware on your device, or have seen evidence that you’ve unknowingly been affected by a bad actor, don’t panic, but you should act quickly.
- Call your bank or credit card company directly to inform them of a potential compromise.
- Scan your computer for malware and viruses. Depending on your device, you may find any number of free or low-cost applications that should help you out until you can fully remediate the damage.
- Change all of your passwords from another device you believe to have not been impacted by this.
Cybercriminals are finding new and more sophisticated ways to exploit a business’s vulnerabilities and break into its systems. If your website has been compromised, it's essential to act quickly to clear your website of malware. Implementing a robust website security solution can help identify and eradicate malicious code while also protecting against future intrusions. Regularly update your content management systems and plugins to patch vulnerabilities and reduce the risk of malware infections.
Key Takeaways
Email is the preferred method of communication in business, thus making it a primary vector for attackers. All it takes for an entire system to be compromised is one single email, resulting in downtime, financial loss or reputational harm.
Maintaining the security of your email has never been more important, or more possible after learning how to differentiate a fraudulent email from a legitimate one. Remember to think before you click, and scan your device often for malware, as these are some of the best practices for preventing your system from being exploited.