There’s a new type of cyberattack that is surreptitiously threatening your systems, your data and your business - and this one lives up to every bit of the danger and sophistication conveyed in its name: fileless malware.
This emerging email-borne threat may sound complex and confusing, but we’re here to break it down for you. Let’s explore the anatomy of a fileless malware attack, and examine some measures that your business can take to avoid falling victim to this hidden threat.
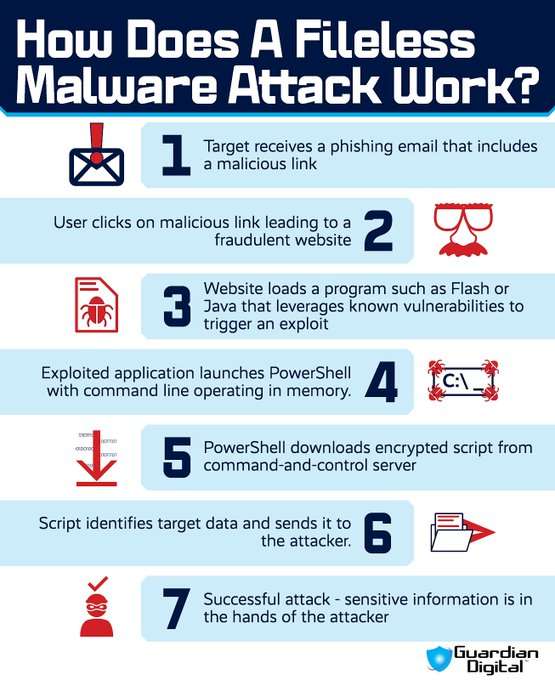
Watch: Step-by-Step Explanation of a Fileless Malware Attack
You may have encountered malware or heard of it terrorizing businesses for a long time, but it is nothing compared to the variant known as S malware, which is much sneakier than traditional malware. For a certain reason, wireless malware differs from standard malware by not using. Files and instead operating in a computer's ram or random access memory to inject malicious codes by using tools trusted by your computer's operating system.
So it is much harder to detect without proper knowledge of file is malware and how it works. It will secretly destroy your company, leaving you confused on how it happened. So Guardian Digital will disclose the anatomy. Of a wireless malware attack to better prepare your company.
Step one, the victim clicks on a phishing link. Wireless malware starts by sending you a phishing email containing information that seems desirable in hopes of deceiving you emails that intend on using file this malware. Always send you a link to a website for you or one of your coworkers to click on so that the attack can progress when proceeding to click on the link to the website in the phishing email, the fraudulent webpage created by the cyber criminal is then loaded from the web browser.
The victim uses
Step two. The sham website loads an application to exploit. Many fraudulent websites are purposefully created with programming software infamous for carrying vulnerabilities like Flash or Java, exploiting them to inject malicious codes into and be put in your web browser's memory.
These applications carry many codes containing programming languages that command your computer instructions. The cybercriminals continue the attack by creating their own code containing commands and putting them in your web browser's plugin application to load the website. Installing a proactive, multi-layered antivirus solution like Guardian Digital OnGuard Cloud email security would stop wireless malware from getting past the first step of this process.
This solution always prevents phishing emails from reaching your inbox without having to even worry about investing in IT resources to keep your software supported. As it comes with managed services to give you a rapid return on investment. Step three, exploited application launches bin with command in memory.
The exploited application used for programming websites through codes now has malicious code injected into it, and the next step is what makes Fileless malware so nerve-wracking: It will turn your operating system's trusted tools against you. These tools are known as living off the land, binaries, or law bins for short, and they are built into your operating system to serve as memory storage for all the codes used to operate.
Your computer and cyber criminals will use these tools like PowerShell, Microsoft Office macros, or WMI. One of these tools are launched once the application contains the malicious command line. And cyber criminals will prepare to use them and simply live off the land as they only use the resources on your computer's territory rather than making their own files.
Step four, encrypted Script identifies target data. After the law bin is launched, it then downloads the malicious code to keep the malware in your computer's memory, which makes this malware much harder to identify and remove as law bins are always whitelisted on every computer. These malicious codes instruct your computer to do harmful actions that usually function along the lines of stealing and sending sensitive data.
To the cyber criminal through its command and control server or even encrypting all files to demand for money. Step five, data is sent to the attacker, which means the attack is successful. As soon as the malicious code is officially downloaded into the law bin, it will begin to function in the way that it was programmed, such as by locating target data and sending it over to the attacker.
In this scenario. Once the sensitive information is now in the hands of the attacker, the attack is officially deemed successful, and the cyber criminals could choose to do as they please with your information.
What Is Fileless Malware and Why Is It A Threat to My Business?
Fileless malware is a payload-less email attack that runs in a computer's random access memory (RAM), not from a malicious file, and exploits existing, trusted system applications to install and run malicious code on target systems. This code is then used to encrypt and exfiltrate sensitive data, transferring it directly into the hands of the attacker. Fileless malware attacks leverage legitimate, trusted operating system tools for malicious purposes, essentially turning systems against themselves.
Fileless malware - which is most commonly delivered in a phishing email - has become a favorite method among cyber criminals of evading security defenses, eavesdropping on corporate networks, compromising systems and gaining access to sensitive data. Ponemon Institute reports that fileless attacks are 10 times more successful than file-based attacks.
The majority of businesses are unprepared to combat this stealthy emerging threat, and are paying the price in data theft, financial loss, reputation damage and system downtime. In recent years, fileless malware has been the culprit of many notorious security incidents, including the 2017 Equifax breach which compromised the personal information of 147.7 million Americans and the 2016 Democratic National Committee (DNC) hack in which confidential documents and emails from Hillary Clinton’s presidential campaign were leaked by the Russian government.
Unlike traditional malware, fileless malware has no signature because it does not leverage executable files. As a result of this evasive technique, signature-based antivirus software and the majority of traditional email security solutions are unable to detect fileless malware and protect businesses’ critical data, accounts and systems from compromise.
Anatomy of a Fileless Malware Attack
Fileless malware attacks are carried out in a series of clearly-defined steps, beginning with the initial lure of a phishing scam and ending with the compromise of sensitive data. Let’s take a look exactly how fileless malware attacks work, step-by-step, to help you better understand this malicious exploit.
Step 1: Victim clicks on a phishing link
Like traditional file-based malware, fileless malware is most commonly distributed via phishing. When a victim clicks on a malicious URL delivered in a phishing email, he or she is unknowingly led to a fraudulent website.
Step 2: Fraudulent website loads an application that triggers an exploit
The fraudulent website loaded by the victim looks for known vulnerabilities in applications such as Flash or Java, which could be exploited to run malicious code in the browser memory. When the website detects a flaw, it launches the vulnerable application and triggers an exploit.
Step 3: Exploited application launches a LOLBin with command line operating in-memory
The exploited program launches a known and trusted built-in operating system tool, or “LOLBin”, such as PowerShell, Microsoft Office Macros, or WMI, with a command line operating in-memory. This advanced, deceptive technique of essential turning systems against themselves by using legitimate, trusted tools for malicious purposes is known as “living off the land”.
Step 4: Encrypted script identifies target data
The LOLBin that has been launched downloads an encrypted script from the command-and-control server operated by the attacker that is designed to identify target data on the victim’s system.
Step 5: Data is sent directly to the attacker = attack successful
Once the script has identified the target data, it sends it directly to the attacker. Unlike other forms of malware, a fileless malware attack leaves no typical footprint on the target system. The system tools exploited in these attacks can’t be removed or disabled, and re
main running on the system until they’re either told to stop by their operators or they eventually render the system inoperable.
How Can I Prevent an Attack?
When it comes to protecting against fileless malware, there are some behaviors and best practices that users should engage in online to mitigate the risk of an attack. They include:
- Make sure that all software and patches are up-to-date.
- Uninstall applications that are not being used and disable unnecessary services and program features for all necessary applications.
- Restrict admin privileges - only grant the privileges that are necessary for a user to do his or her job.
- Monitor network traffic and check activity logs frequently.
- Require that employees take part in security awareness training.
- In the event that an infection does occur, change passwords immediately once you become aware of the infection and again after disinfection.
- Critically important: Implement a proactive, layered supplementary email security solution that provides real-time protection against fileless malware and other sophisticated modern cyberattacks by creating a safeguarded environment around the user. Selecting a solution that is accompanied by managed services can simplify administration, enhance security and free up valuable IT resources - delivering a rapid return on investment (ROI).
The Bottom Line
Safeguarding your critical assets - and your business as a whole - from fileless malware and other emerging exploits requires adaptive, layered email security defenses. There is an ongoing “cat and mouse” game at play between cyber criminals and security companies - as security defenses evolve, attackers continue to develop new ways to “outsmart” providers. The key best practices like firewall implementation and firewall change management systems can offer consideration protection from attackers. Likewise, cybersecurity awareness can help, but fileless malware attacks are unprecedented. Thus, in order to fortify business email against today and tomorrow’s threats, it is imperative that organizations implement a solution that is constantly learning from the threats that challenge it, and rapidly updating its protection to protect against the latest, most evasive attacks.
Have additional questions about fileless malware? We’re here to help! Leave a comment below and one of our security experts will be in touch with you shortly.