Ransomware lands where there are detection gaps. It only takes one foothold to start encrypting files and backing teams into ransom talks. Below is a structured breakdown of ransomware detection methods and supporting controls to reduce impact:
Understanding Ransomware and Its Impact on Businesses
Ransomware encrypts files or locks systems, then demands payment for restoration. Once it executes, the clock starts. Encryption spreads across mapped drives, backup repositories, and anything the compromised account can reach. It does not just hit big companies. Small clinics, local governments, and mid-sized manufacturers are all targets.
Operations stall first. Shared drives go read-only. Line-of-business apps fail. Then legal gets involved, regulators will need to investigate data encryption policies, and at-risk customers will demand answers. Recovery is not just about restoring files, but proving how well the attack was contained.
This is where ransomware detection matters. Early identification cuts down attacker dwell time and slows lateral movement before encryption spreads across shared drives and critical systems.
Traditional Ransomware Detection Techniques 
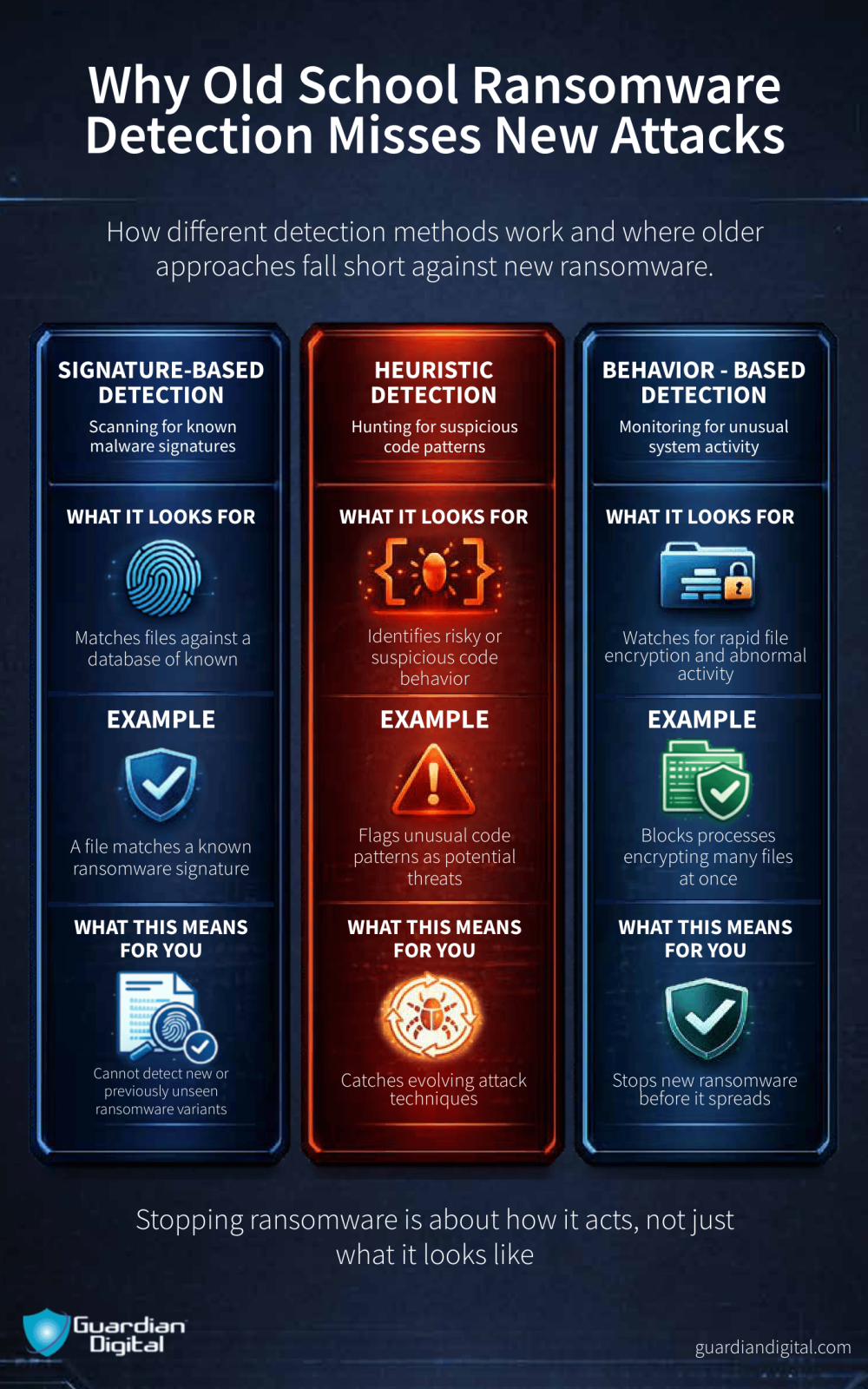
For data breach prevention to be reliable, organizations must understand how to use layered detection methods. Most traditional ransomware detection methods rely on known patterns, rule sets, and steady system monitoring. They work well against threats we have already seen and analyzed. The problem is that attackers iterate fast, and these controls usually need yesterday’s sample to stop today’s variant.
Signature-based Ransomware Detection
Signature-based detection compares files against a database of known ransomware signatures. If there is a match, the file gets quarantined or blocked before it runs.
It works well for documented families and anything tied to established ransomware service operations that reuse tooling across affiliates. A lot of commodity campaigns still fall into this bucket.
The weakness is obvious. New builds, minor code changes, or heavy obfuscation can slide past until signatures catch up. Zero-day payloads and custom loaders do not care about yesterday’s hash list.
Heuristic-based Ransomware Detection
Heuristic-based detection is basically pattern watching without a hard signature. It does not care if the file hash is brand new. It cares if something starts acting wrong.
If a process begins encrypting files in bulk, tries to bump its privileges, or shuts off security tools, that is a red flag. We have rules in place that say, this behavior is not normal for a standard user process, so flag it or stop it.
It helps with new variants because attackers can change code fast, but they still need to encrypt files and mess with the system to get paid. That part does not change much.
The catch is noise. A legit software rollout or a large file migration can look aggressive, too. If heuristics are not tuned to recognize those scenarios, then they will waste time and energy on harmless alerts.
Behavior-based Ransomware Detection
Behavior-based detection goes deeper into what the endpoint is doing in real time. It watches processes, file writes, and memory use. All the messy details.
When something suddenly touches hundreds of files in seconds, spawns command shells it should not need, or chews CPU in a way that lines up with encryption routines, the agent steps in. In a good scenario, it kills the process and isolates the host before the damage spreads to shared drives.
This is where ransomware detection proves its value during a live incident. There is no delay waiting on a signature update to roll out across endpoints. The response is driven by what is happening in real time on the affected system.
Accurate baselining is critical. Backup agents, patching scripts, and administrative tools often generate heavy file activity and elevated processes that look aggressive on the surface. Without a clear understanding of normal behavior, security teams risk blocking legitimate business operations or allowing actual encryption activity to blend into routine system noise.
Advanced Ransomware Detection Techniques 
Traditional controls catch what we already know about. Advanced techniques try to catch what we have not seen yet. Done right, this supports data breach prevention by flagging not just ransomware encryption behavior, but also the exfiltration activity that often comes first.
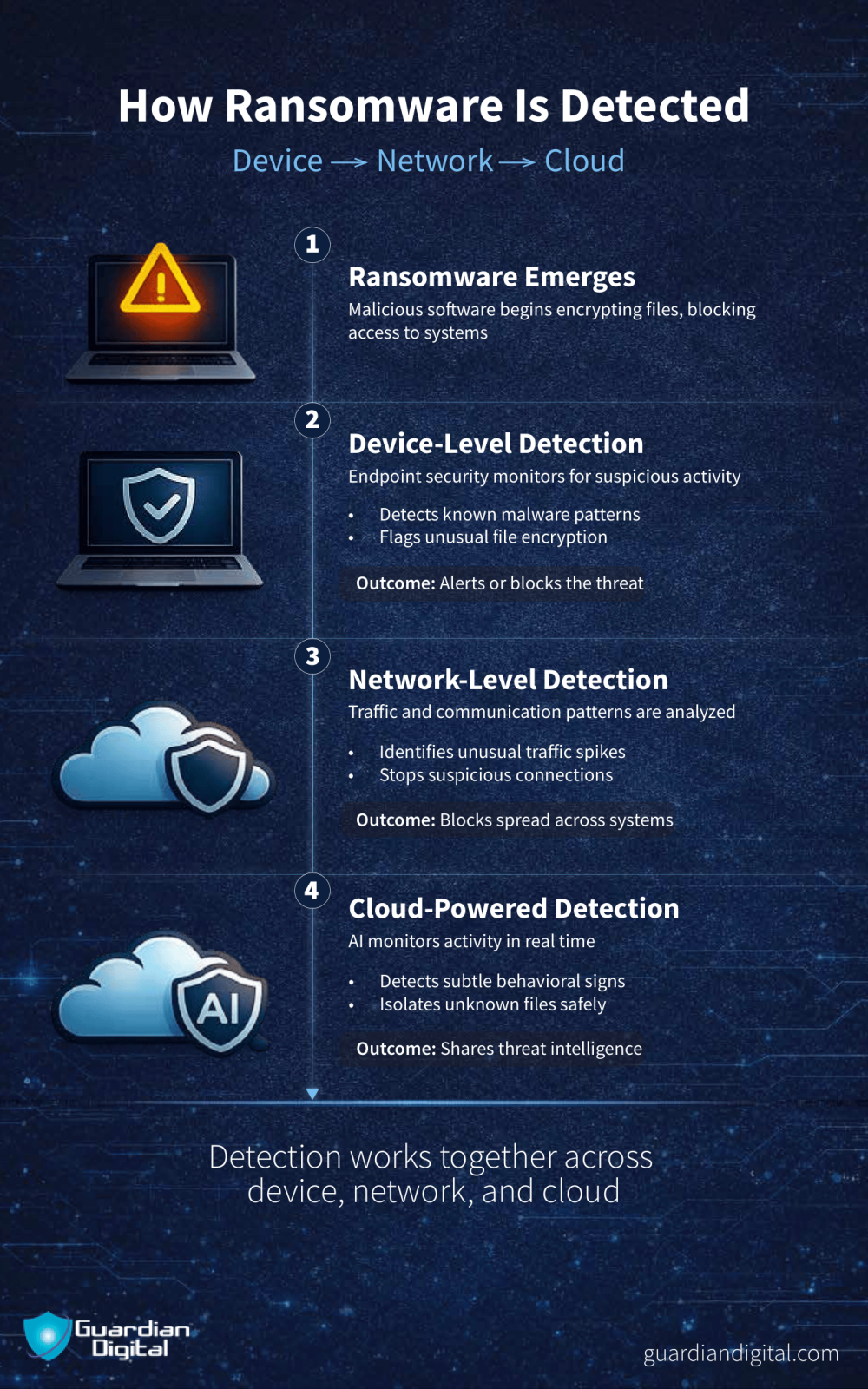
Ransomware Detection with AI and Machine Learning
AI and machine learning models are trained on past attack data and live behavioral signals. They examine how files are accessed, how users authenticate, and how traffic normally flows within the network.
When something drifts from that baseline, like a service account suddenly accessing finance shares at 3 a.m. and spawning encryption routines, it gets scored as risky. The system does not need a known signature. It needs enough deviation to say this is not normal.
Mature setups automate part of the response. If risk scores pass a defined threshold, the model knows how to shut down the offending process and contain its spread. Early containment saves shared infrastructure from data breaches.
The models get sharper as they ingest more telemetry across endpoints, identities, and network flows. They are not self-running systems though. Tuning, validation, and regular review are still required if they are expected to catch new ransomware strains that reuse familiar tactics with slightly modified code.
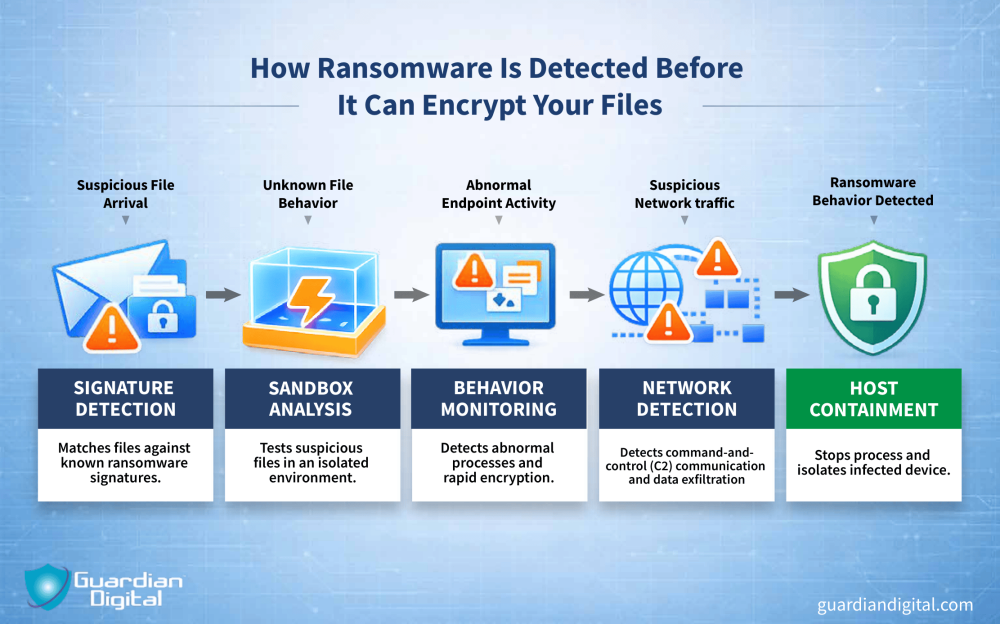
Sandboxing & Ransomware Detection
Sandboxing is a method for running a suspicious file in a safe place that will not expose the rest of the system.
The file executes in an isolated environment where it can only encrypt dummy files, reach out to command and control servers, or modify system settings without touching production systems. If it behaves like ransomware, it never makes it to a user’s machine.
This is especially useful for analyzing a phishing attack payload before release. Instead of trusting a quick scan, SOC can watch what the attachment actually does when opened.
The main limitation of sandboxing is that it adds time and computing overhead, and not every file can be detonated at scale. But against weaponized Office docs or script-based loaders, having that controlled detonation environment is worth it.
Detection Strategies 
No single sensor catches everything. Real ransomware detection works when host and network telemetry are tied together, not living in separate dashboards that no one correlates.
IT teams need visibility across endpoints and traffic flows at the same time. That means aligning EDR data with what IDS or NDR sees and integrating it into network security strategies rather than treating it as an add-on.
When anomalies line up across multiple control points, the response gets clearer. A suspicious process on a host plus strange outbound traffic is not a coincidence. It is a containment decision. Early containment is the difference between isolating one workstation and rebuilding half the environment.
Network-based Detection
Network-based detection watches outbound connections and traffic patterns. It looks for endpoints talking to known bad infrastructure or suddenly pushing large volumes of data to unfamiliar destinations.
Ransomware operators often stage payloads or exfiltrate data before encryption. If IDS or NDR flags traffic to blacklisted domains or command and control servers, the business network gets a warning before users notice locked files.
Traffic spikes matter too. A workstation that normally checks email and browses the web should not suddenly generate sustained encrypted sessions to an IP in a region the company never touches.
Block the connection. Alert the SOC. Then pivot to the host and figure out what started it.
Host-based Detection
Host-based detection lives on the endpoint. It watches file system changes, process creation, privilege use, and registry edits. The gritty stuff.
When a process starts modifying hundreds of files in seconds or spawning command shells from an Office document, the agent should step in. Ideally, it kills the process and isolates the device before shared drives are encrypted.
This layer is critical for containing the spread inside the network. Once ransomware lands on one machine, it will probe for accessible shares and cached credentials across multiple systems.
Best Practices for Ransomware Detection
Ransomware detection on its own is not a strategy. Unless detection is tied to recovery planning and business continuity, alerts are not enough to change the outcome.
Backup and Disaster Recovery Strategy
A real backup and disaster recovery strategy defines who does what when ransomware starts encrypting the system. Escalation paths, isolation procedures, and communication plans should be rehearsed ahead of the actual attack. That foundation makes ransomware recovery possible without improvising under pressure.
Backups need to be off-site and ideally immutable, because if attackers can access the backup repository, they will encrypt that too. They also need regular restoration testing to prove how fast critical systems can get back online.
An effective ransomware backup and recovery strategy enables teams to wipe infected systems, restore them cleanly, and move on without paying the ransom.
Software and Patch Management
Ransomware campaigns still lean on known weaknesses: unpatched VPN appliances, outdated web servers, and exposed RDP services. Patch management shuts those doors before they get tested. It trims the attack surface across operating systems, third-party software, and network gear that attackers routinely scan for.
Regular updates are not busywork. They are one of the most practical controls in ransomware defense. Fewer exposed entry points means fewer footholds, and fewer footholds means fewer incidents reaching the detection stage at all.
Employee Education & Email Security Awareness
Most ransomware incidents still start with a phishing email. A fake invoice. A shared document link. A request that looks routine until it is not.
Structured email security training helps staff recognize those patterns before they click. It is not about turning employees into analysts. It is about slowing down the attacker’s easiest path in.
Simulated phishing campaigns reinforce that muscle memory. Users see how real lures look, and the SOC gets data on who needs more coaching.
Training strengthens the human layer alongside technical email security controls. Users who report suspicious messages instead of interacting with them cut off initial access. In addition to stopping ransomware, awareness supports broader data breach prevention efforts before malware ever touches an endpoint.
Ransomware Detection FAQ 
Let’s review a few common questions about how ransomware detection works:
What is the most effective ransomware detection method?
The most effective setups use multiple controls. They layer endpoint behavior monitoring with network visibility and solid email security.
How quickly can ransomware detection systems identify a threat?
Well-tuned systems detect ransomware in seconds to minutes. Weak logging or excessive alerts will make detection take longer.
Can ransomware detection tools protect against brand-new ransomware variants?
Signature-based detection alone cannot detect new types of ransomware, but behavior-based controls can detect variants because of the actions they take.
How does sandboxing work for ransomware detection?
Potentially harmful files get detonated in a safely contained environment. Anything that attempts to encrypt files will get blocked before it ever hits a real user system.
Can cloud-based security systems detect ransomware across multiple devices?
Yes, if they are pulling telemetry from all those devices. When one host starts acting strange, the platform can flag similar behavior elsewhere. Visibility helps to contain ransomware faster.
Keep Learning About Ransomware Detection
Ransomware crews change tactics regularly. Therefore, businesses need a ransomware detection stack where signature scans, behavioral rules, smart analytics, and email security are cohesively layered.
It’s equally important to have a recovery plan ready to kick in when detection is not fast enough. Clear escalation paths, people who know their roles, and regularly tested backups are the key to keeping incidents contained. Ransomeware and data breach prevention work best when SOC teams anticipate persistent attacks and prepare to overcome them.