Phishing usually goes wide. One message, a long recipient list, and the attacker waits for somebody to click before they think. A login page. A file download. A payment approval. Sometimes just a reply.
Spear phishing is tighter. The attacker does some homework first, then builds the message around a person, role, vendor, invoice, meeting, or workflow that already exists inside the company.
That is where the risk changes. A generic phishing email may look suspicious fast. A spear phishing email can land inside normal work and stay there long enough to do damage.
Finance gets a vendor note. IT gets an account alert. HR gets an attachment. Someone in leadership gets asked to approve something that sounds routine enough, until the money moves or the mailbox is gone.
Today, we will break down how phishing works, where spear phishing becomes harder to catch, and why both still create problems for businesses even after years of security training.
What Are Phishing Attacks?
Phishing attacks trick users into giving up credentials, money, files, or access. Most of them look like routine messages because routine messages get opened.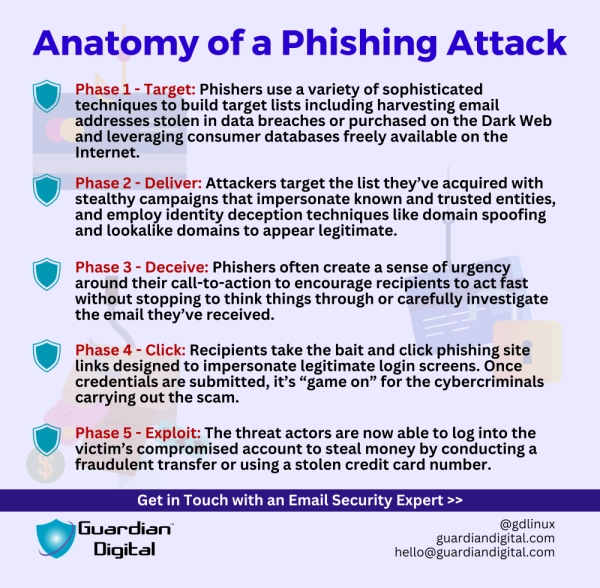
Password resets. Bank notices. Shipping updates. Microsoft 365 prompts. Shared document alerts. Fake security warnings. Nothing dramatic, usually. Just enough pressure to make someone act before they slow down.
The volume is the point. A phishing campaign does not need a high success rate. If one person enters credentials on a fake page, the attack has already done its job.
That is why broad phishing still works. It does not need to fool the whole company. It needs one rushed employee on the wrong afternoon.
How Phishing Threats Have Changed
Modern phishing looks cleaner than it used to. The old signs still show up, but they are less reliable now.
Attackers use cloned login pages, fake MFA prompts, QR codes, file-sharing notices, compromised accounts, and AI-written messages that read well enough to survive a quick scan. The grammar may be fine. The branding may look close. The sender may even be a real account that was compromised earlier.
That changes the detection problem. Employees were taught to look for broken language, strange formatting, and suspicious links. Useful checks, but not enough anymore.
Modern phishing threats often look like normal business communication. That is the issue.
What Is a Spear Phishing Attack?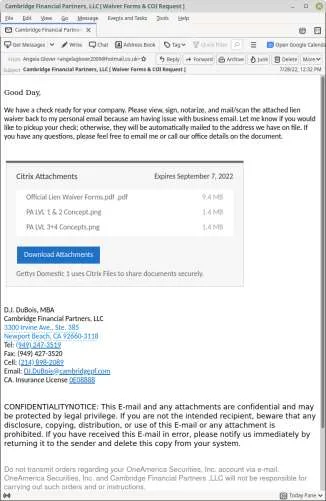
A spear phishing attack is built for a specific target. The attacker may focus on one employee, one department, one company, or one role with useful access.
The research comes first. LinkedIn, company pages, press releases, social media, breach data, job postings, vendor relationships, and old compromised email threads all help attackers build a message that feels relevant.
Finance gets a billing update. HR gets a resume. IT gets an account warning. An executive assistant gets a confidential request from someone pretending to be leadership.
That is why a spear phishing attack is harder to dismiss. It does not feel random. It fits the workflow.
Spear Phishing vs. Phishing
The core difference is targeting.
Phishing goes broad. Spear phishing narrows the attack around a person, job function, or business process.
A phishing email may say an account is locked and ask the user to verify a password. A spear phishing email may reference a real vendor, manager, invoice, department, project, or meeting.
That small layer of context changes employee behavior. People question random messages. They question familiar ones less.
Phishing looks for anyone willing to click. Spear phishing looks for the person whose click opens the right door.
How to Spot Phishing and Spear Phishing Emails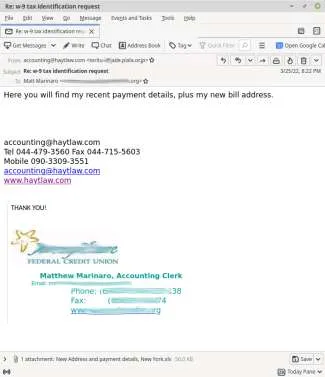
The sender address is not always enough. Sometimes the domain is spoofed. Sometimes it is a lookalike. Sometimes the attacker is using a real mailbox, which makes the message harder to flag at a glance.
Look at the request instead. Payment changes. Password prompts. Shared files. QR codes. Banking updates. Confidential instructions. Anything urgent, unusual, or outside the normal process needs more scrutiny.
Tone helps too. A message that suddenly pushes secrecy, speed, or bypassed approval should slow things down.
The best check is still basic. Does this match how the company normally handles this type of request? If not, verify it somewhere other than the email thread.
Spear Phishing Example: 2026 Microsoft 365 Device Code Campaign
A good 2026 spear-phishing example is the device code phishing campaign that Microsoft reported in April.
The emails were not generic password-reset junk. Microsoft said the lures were shaped around the victim’s role, using themes like RFPs, invoices, document access, electronic signing, voicemail notifications, and manufacturing workflows. Normal business bait. The kind employees already deal with all week.
The trick was the login flow. Instead of asking users to type a password into an obvious fake Microsoft page, the attacker pushed them toward Microsoft’s legitimate device login process. The victim entered a code, approved the sign-in, and the attacker received access tokens on the backend. MFA was not “broken” so much as worked around through a different authentication path.
That is what makes the case useful. The phishing email did not need to look wild. It just had to get the user to follow a process that felt close enough to normal.
CSA put the scale at 340+ Microsoft 365 organizations by mid-March 2026. The affected sectors were not narrow either: construction, nonprofits, real estate, manufacturing, financial services, healthcare, legal services, and local government all showed up in the reporting.
After the compromise, Microsoft said attackers looked for higher-value users, including financial, executive, and administrative roles. They searched for wire transfer details, pending invoices, and executive correspondence. That is where spear phishing turns from credential theft into business email compromise. Quietly. Usually, after the first click, it already looks like old news.
Business Risks From Phishing Attacks
Phishing attacks targeting businesses can lead to account takeover, wire fraud, payroll diversion, ransomware, data theft, and business email compromise.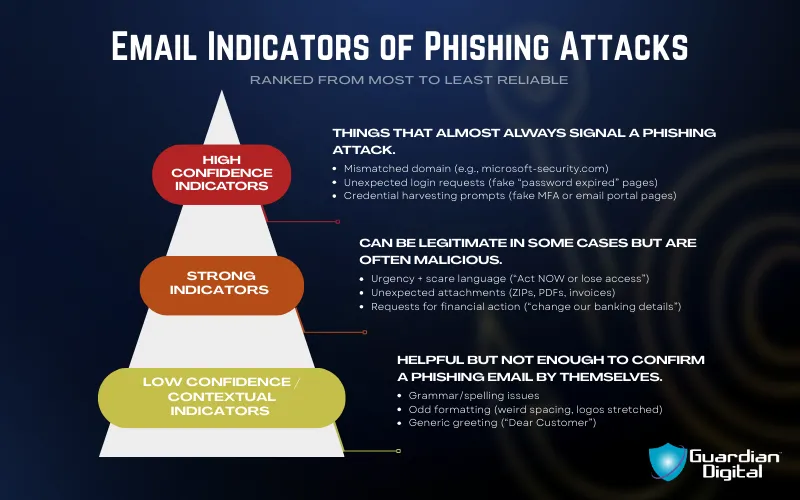
A single employee mailbox can expose more than people expect. Vendor conversations. Customer files. Shared drives. Payment systems. Admin tools. Internal approvals. Once attackers get inside a trusted account, they can reuse that trust against the business.
A consumer phishing scam may steal one password. A business phishing attack can compromise a workflow.
That is why broad phishing attacks still deserve attention. Even a generic email becomes dangerous when it lands in the right inbox.
Why Spear Phishing Targets High-Value Employees
Attackers target people who can approve, access, influence, or move a request forward.
Executives. Finance teams. Payroll staff. HR. IT admins. Legal teams. Procurement. Executive assistants. These roles sit close to systems and decisions that attackers want to reach.
The target is not always the most senior person. Sometimes it is the person with the least friction in the process. Someone who can update payment information, reset an account, share a file, or approve a request without drawing attention.
A compromised finance account can expose payment workflows. A compromised IT account can support lateral movement. A compromised executive mailbox can make fraud look internal.
Access matters more than title.
How to Prevent Phishing Attacks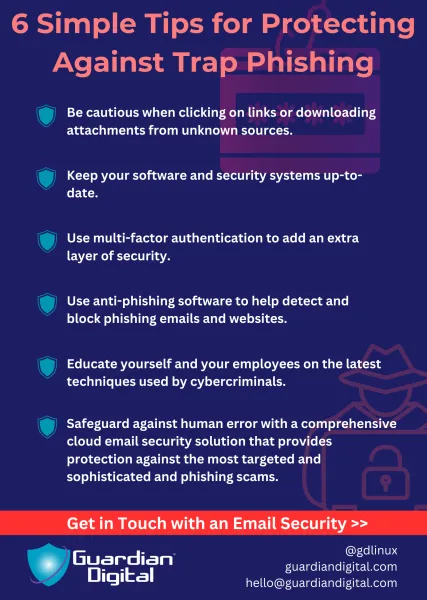
Start with controls that remove easy wins. Use MFA. Enforce strong passwords. Stop password reuse. Configure SPF, DKIM, and DMARC. Train employees to verify unusual requests outside the original email thread.
Then focus on the workflows attackers keep abusing. Payment changes. Payroll updates. Vendor invoices. Shared documents. Executive requests. Password resets. These need clear verification steps, not informal judgment calls made during busy work.
Security awareness helps, but it cannot carry everything. Some phishing emails look too normal now. Email security has to look at the whole message now, not just the obvious bad link. Sender behavior, attachment risk, impersonation signals, authentication results, strange login activity, and what the user is being asked to do all matter together.
That changes the goal a bit. Phishing prevention is not just teaching people to spot ugly phishing emails anymore. It is building enough checks around email that one believable message cannot carry the full weight of trust.
The Bottom Line
Phishing and spear phishing both exploit trust. The difference is how much work the attacker does before sending the message.
Phishing sends broad messages and waits for someone to respond. Spear phishing studies the target, then builds a message around the person, role, company, or workflow.
That extra context raises the risk. Spear phishing usually gets closer to financial approvals, executive inboxes, payroll systems, vendor relationships, cloud accounts, and internal documents.
The emails may not look dangerous. Many look routine. That is exactly why they keep working.
Strong defense depends on slower approvals, better verification habits, layered email security, and employees who are allowed to challenge unusual requests without treating them like a delay.
FAQs
How do I know if an email is spear phishing?
Look for context that feels a little too fitted to you.
A spear phishing email may mention your manager, vendor, department, invoice, open role, project, or a real workflow inside the company. That does not make it safe. It may just mean the attacker did homework before sending it.
Slow down anything asking for credentials, money, file access, payroll changes, or confidential action. Verify through another channel.
Is spear phishing worse than regular phishing?
Usually, yes.
Regular phishing is more of a volume play. Spear phishing is built around the target, so the message tends to feel more believable and can land closer to sensitive systems.
That is where the damage changes. A broad phishing email might steal a password. A good spear phishing email can lead to payment fraud, account takeover, vendor compromise, or lateral movement if it hits the right person.
Can phishing emails come from real accounts?
Yes, and that is one of the harder parts.
Attackers often use compromised mailboxes to send phishing emails from accounts people already trust. The sender looks legitimate because, technically, it is. The problem is that the person behind the keyboard has changed.
That is why sender checks alone are weak. The request matters more.
What should employees do with a suspicious email?
Do not reply to the thread. Do not click the link just to “check.” Do not scan the QR code because it looks harmless.
Report it through the company’s normal process, then verify the request separately if it involves money, credentials, access, or sensitive data. A phone call or internal chat message can stop a lot of damage.
Simple, but it works.
How can small businesses reduce phishing risk?![]()
Start with the controls that block common failures. MFA, strong passwords, no reused credentials, SPF, DKIM, DMARC, and clear reporting paths.
Then lock down the business processes, attackers like most. Payment changes, payroll updates, vendor invoices, password resets, and executive requests should not move on email alone.
Small teams do not need a huge program to improve. They need fewer informal exceptions.
For the full article, I’d also break the section pattern harder. Some sections should open with an example. Some should start with the conclusion. Some should skip the tidy “why it matters” ending. The whaling sample does this better because it lets a few sections run like notes from an investigation instead of forcing every heading into the same mold.
What Is QR Code Phishing?
QR code phishing moves the click somewhere else.
Instead of putting a visible link in the email, the attacker drops in a QR code and waits for the user to scan it with a phone. From there, the page may copy a Microsoft 365 login, a payment portal, a secure document request, or some internal access screen.
It feels harmless because the email itself may not have much to inspect. No ugly URL sitting in plain view. Just a square image and a reason to scan it.
That creates a visibility gap. Email tools are usually better at checking links than reading intent from an image, and once the user moves to a mobile device, the company may have less control over what happens next.
 What Is Trap Phishing?
What Is Trap Phishing?
Trap phishing pushes users into a fake process that feels legitimate.
The trap may be a support portal, password reset page, account verification prompt, subscription renewal notice, or shared file request. The user thinks they are solving a routine problem. The attacker is collecting the login, payment details, or sensitive information.
The email is often just the entry point. The real compromise happens after the click, once the victim is inside a workflow that looks normal enough to trust.
Phishing is not always one bad message anymore. Sometimes it is a fake business process.